How to install aircrack-ng on Solus OS Linux [detailed manual]
Before we start installing aircrack-ng, let's read, what they write on the official website:
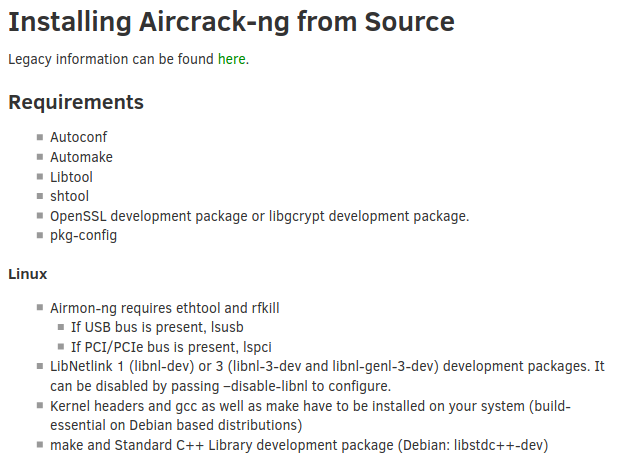
For those, who don't want to download images:
Requirements
Autoconf
Automake
Libtool
shtool
OpenSSL development package or libgcrypt development package.
pkg-config
Linux
Airmon-ng requires ethtool and rfkill
If USB bus is present, lsusb
If PCI/PCIe bus is present, lspci
LibNetlink 1 (libnl-dev) or 3 (libnl-3-dev and libnl-genl-3-dev) development packages. It can be disabled by passing –disable-libnl to configure.
Kernel headers and gcc as well as make have to be installed on your system (build-essential on Debian based distributions)
make and Standard C++ Library development package (Debian: libstdc++-dev)
So, in order to be sure aircrack will work on our machine, we have to meet requirements and ensure that we have all required programmes installed. It's better to do it now, because during the process of installation of aircrack-ng we potentially will have problems, because of missing sw or libraries.
Let's check, if we have everything:
Autoconf
$ autoconf -V
autoconf (GNU Autoconf) 2.69
Copyright (C) 2012 Free Software Foundation, Inc.
License GPLv3+/Autoconf: GNU GPL version 3 or later
<http://gnu.org/licenses/gpl.html>, <http://gnu.org/licenses/exceptions.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Written by David J. MacKenzie and Akim Demaille.
Automake
$ automake --version
Copyright (C) 2020 Free Software Foundation, Inc.
License GPLv2+: GNU GPL version 2 or later <https://gnu.org/licenses/gpl-2.0.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Written by Tom Tromey <tromey@redhat.com>
and Alexandre Duret-Lutz <adl@gnu.org>.
Libtool
$ libtool --version
libtool (GNU libtool) 2.4.6
Written by Gordon Matzigkeit, 1996
Copyright (C) 2014 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
shtool
Read: How to install GNU shtool in Solus OS Linux
openSSL
Let's check, if we have it:
$ openssl
OpenSSL> version
OpenSSL 1.0.2u 20 Dec 2019
Good.
pkg-config
Let's check, if we have it:
$ pkg-config --version
0.29.2
Good, now we have all and can install aricrack-ng itself:
Installing aircrack-ng
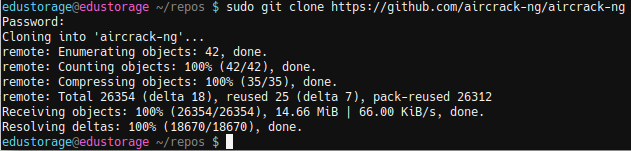
Again, clone repository:
$ sudo git clone https://github.com/aircrack-ng/aircrack-ng
Then we are running following command, just like they write it on official website:
$ cd aircrack-ng
$ sudo autoreconf -i
output:
libtoolize: putting auxiliary files in AC_CONFIG_AUX_DIR, '.'.
libtoolize: copying file './ltmain.sh'
libtoolize: putting macros in AC_CONFIG_MACRO_DIRS, 'build/m4/stubs'.
libtoolize: copying file 'build/m4/stubs/libtool.m4'
libtoolize: copying file 'build/m4/stubs/ltoptions.m4'
libtoolize: copying file 'build/m4/stubs/ltsugar.m4'
libtoolize: copying file 'build/m4/stubs/ltversion.m4'
libtoolize: copying file 'build/m4/stubs/lt~obsolete.m4'
configure.ac:85: installing './compile'
configure.ac:58: installing './config.guess'
configure.ac:58: installing './config.sub'
configure.ac:69: installing './install-sh'
configure.ac:69: installing './missing'
Makefile.am: installing './depcomp'
parallel-tests: installing './test-driver'
Ok, configured. Then we run command in order to check, if we have everything:
$ sudo ./configure --with-experimental
my output:
Build Environment:
Build Machine: x86_64-pc-linux-gnu
Host Machine: x86_64-pc-linux-gnu
Target Machine: x86_64-pc-linux-gnu
Install Prefix: /usr/local
Compiler Environment:
C Compiler: gcc
C++ Compiler: g++
Python: python
CFLAGS:
CXXFLAGS:
CPPFLAGS: -D_FORTIFY_SOURCE=2
LDFLAGS:
LIBS: -ldl -lm
Optimized CFLAGS: -Wall -O3 -std=gnu99 -fno-strict-aliasing -Wpointer-arith -Wstrict-overflow=2 -Wstrict-prototypes -fvisibility=hidden -fstack-protector-strong -Wno-unused-but-set-variable -Wno-array-bounds
Optimized CXXFLAGS: -Wall -O3 -fvisibility=hidden -fstack-protector-strong -Wno-unused-but-set-variable -Wno-array-bounds -masm=intel
Optimized CPPFLAGS:
Optimized LIBS:
Target Environment:
OS: linux
ASAN: no
CPU L1 cache-line size: 64
Crypto Libraries:
Crypto Engine: openssl
Gcrypt:
OpenSSL: -lssl -lcrypto
Required Libraries:
Ethtool: not found, skipping Airmon-ng
Libnl: no
Optional Libraries:
Airpcap: no
Cmocka: no
DUMA: no
Hwloc: no
Jemalloc: no
Pcap: no
Pcre: yes
Sqlite: no
Tcmalloc: no
Zlib: yes
Features:
CMAC Support: yes
Experimental Extra Scripts: no
Experimental Features: yes
You see, I didnt' install optional libraries.
Then:
$ sudo make
$ sudo make install
Output is very big, I will not publish it here.
Let's check, if aircrack-ng was installed:
$ cd aircrack-ng
$ sudo ./aircrack
output:
Aircrack-ng 1.6 rev c4981c71 - (C) 2006-2020 Thomas d'Otreppe
https://www.aircrack-ng.org
usage: aircrack-ng [options] <input file(s)>
Common options:
-a <amode> : force attack mode (1/WEP, 2/WPA-PSK)
-e <essid> : target selection: network identifier
-b <bssid> : target selection: access point's MAC
-p <nbcpu> : # of CPU to use (default: all CPUs)
-q : enable quiet mode (no status output)
-C <macs> : merge the given APs to a virtual one
-l <file> : write key to file. Overwrites file.
Static WEP cracking options:
-c : search alpha-numeric characters only
-t : search binary coded decimal chr only
-h : search the numeric key for Fritz!BOX
-d <mask> : use masking of the key (A1:XX:CF:YY)
-m <maddr> : MAC address to filter usable packets
-n <nbits> : WEP key length : 64/128/152/256/512
-i <index> : WEP key index (1 to 4), default: any
-f <fudge> : bruteforce fudge factor, default: 2
-k <korek> : disable one attack method (1 to 17)
-x or -x0 : disable bruteforce for last keybytes
-x1 : last keybyte bruteforcing (default)
-x2 : enable last 2 keybytes bruteforcing
-X : disable bruteforce multithreading
-y : experimental single bruteforce mode
-K : use only old KoreK attacks (pre-PTW)
-s : show the key in ASCII while cracking
-M <num> : specify maximum number of IVs to use
-D : WEP decloak, skips broken keystreams
-P <num> : PTW debug: 1: disable Klein, 2: PTW
-1 : run only 1 try to crack key with PTW
-V : run in visual inspection mode
WEP and WPA-PSK cracking options:
-w <words> : path to wordlist(s) filename(s)
-N <file> : path to new session filename
-R <file> : path to existing session filename
WPA-PSK options:
-E <file> : create EWSA Project file v3
-I <str> : PMKID string (hashcat -m 16800)
-j <file> : create Hashcat v3.6+ file (HCCAPX)
-J <file> : create Hashcat file (HCCAP)
-S : WPA cracking speed test
-Z <sec> : WPA cracking speed test length of
execution.
SIMD selection:
--simd-list : Show a list of the available
SIMD architectures, for this
machine.
--simd=<option> : Use specific SIMD architecture.
<option> may be one of the following, depending on
your platform:
generic
avx512
avx2
avx
sse2
altivec
power8
asimd
neon
Other options:
-u : Displays # of CPUs & SIMD support
--help : Displays this usage screen
Yep, everything went good!