How to brute-force .hccapx file using hashcat (Brute-force attack) in openSUSE Linux [with screenshots]
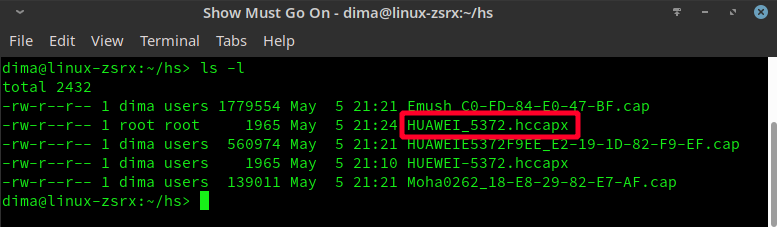
Once you have captured WPA handshake and you've got .cap file, you have to convert given .cap file to .hccapx file format in order to brute force it. There're a lot of approaches, how to successfully crack wi-fi passwords. You never know, what is the structure of a password a surely you won't have enough equipment to crack a long password. In my case I'm trying to brute-force a password supposing it's only 8 digits long, because I know exactly, that the owner of a modem is using a model, which has by default only 8-digits password.
Yes, there's a possibility, that he configured his wi-fi modem manually and changed a password for more secure one, but there's also a chance he's just using it "as is". My computer will crack 8-digits long password in several minutes and I'm going to try to do it. In case I'm not successful, I will think about using dictionaries, because cracking even 8 character long password (digits, letters, capitals, special symbols) will take me years to crack.